👇🏻 이전글 참고
Cloud9에서 키페어 생성 후 AWS에 등록
키페어를 생성하는 방법에는 다음의 두 가지 방법이 있다. 1. AWS 콘솔에서 키페어 생성 -> Cloud9 인스턴스로 가지고 오기 2. Cloud9 인스턴스에서 키페어 생성 -> AWS에 등록하기 우리는 2번째 방법(SSH
taetoungs-branch.tistory.com

0. provider 지정
provider "aws" {
# access_key = "자신의 Key 를 입력" # Cloud9 을 사용하면 IAM Role 을 활용하게 됩니다. 만일 Mac 사용자는 IAM 에서 발급해야 합니다.
# secret_key = "자신의 Key 를 입력"
region = "ap-northeast-2"
}테라폼에서 사용하는 provider란 AWS, Azure, GCP 등을 말한다. 아래의 링크에서 확인할 수 있다.
Terraform Registry
registry.terraform.io
access key, secret key가 있는 경우 속성값으로 입력할 수 있다. 현재 실습에서는 Cloud9에서 AWSCloud9SSMInstanceProfile Role을 사용하므로 생략한다.
1. AWS에 public key 등록
# aws에 import하는 명령어랑 같은거 -> 이미 같은 이름의 키페어가 업로드되어있으면 충돌남
resource "aws_key_pair" "key-pair" {
key_name = "terraform-key"
public_key = file("/home/ec2-user/.ssh/tf-key.pub")
}이전 글에서 AWS CLI 명령어를 사용해서 Cloud9에 위치한 public key를 import해주는 명령어와 동일한 작업을 수행한다.
public key를 하드코딩으로 직접 넣어줄 수도 있겠지만 보안상 그렇게 사용하지 않는다. 이 코드에서는 Cloud9의 /home/ec2-user/.ssh 디렉토리에 있는 public key파일을 참조하도록 작성했다.
2. AMI 지정
data "aws_ami" "amzn2" {
most_recent = true
filter {
name = "name"
values = ["amzn2-ami-hvm-2.0.*-x86_64-gp2"]
}
filter {
name = "virtualization-type"
values = ["hvm"]
}
owners = ["amazon"] # Canonical
}AWS에서 가장 최근의 Amazon Linux 2, HVM 가상화, x86_64 아키텍처, gp2 볼륨 타입을 가진 AMI 정보를 가져온다.
3. 보안그룹 생성
resource "aws_security_group" "sg_web" {
name = "sg_web"
description = "Allow web inbound traffic"
vpc_id = "<VPC ID>" # 사용하고자하는 VPC ID 입력
ingress {
description = "Web from VPC"
from_port = 0
to_port = 0
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
tags = {
Name = "allow_web"
}
}👇🏻 명령어 설명
해당 테라폼 코드는 AWS에 보안 그룹을 생성하기 위한 코드입니다. 각 부분에 대해 상세하게 설명하겠습니다.
1. 기본 정보 :
resource "aws_security_group" "sg_web" {
name = "sg_web"
description = "Allow web inbound traffic"
vpc_id = "<VPC ID>" # 사용하고자하는 VPC ID 입력
- `resource "aws_security_group" "sg_web"`: AWS 보안 그룹 리소스를 생성하는 선언입니다. 이 리소스의 local name은 "sg_web"입니다.
- `name`: 생성될 보안 그룹의 이름입니다.
- `vpc_id`: 해당 보안 그룹이 연결될 VPC의 ID입니다. `<VPC ID>`는 실제 VPC ID로 변경해야 합니다.
2. 수신 규칙 (Ingress) :
ingress {
description = "Web from VPC"
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
- `from_port` 및 `to_port`: 수신을 허용하는 포트 범위입니다. 여기서는 0으로 설정되어 있어 실제 포트 정보가 누락되었을 가능성이 있습니다.
- `protocol`: "-1"은 모든 프로토콜을 허용한다는 의미입니다.
- `cidr_blocks`: 수신을 허용하는 IP 주소 범위입니다. "0.0.0.0/0"은 모든 IP 주소에서의 접근을 허용함을 의미합니다.
3. 발신 규칙 (Egress) :
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
- `from_port` 및 `to_port`: 발신을 허용하는 포트 범위입니다. 0으로 설정되어 있으나, 프로토콜이 "-1"로 설정되어 있어 모든 포트를 의미합니다.
- `protocol`: "-1"은 모든 프로토콜을 허용한다는 의미입니다.
- `cidr_blocks`: 발신을 허용하는 IP 주소 범위입니다. 여기서도 "0.0.0.0/0"은 모든 IP 주소로의 접근을 허용함을 의미합니다.
4. 태그 (Tags) :
tags = {
Name = "allow_web"
}
- `tags`: AWS 리소스에 추가할 수 있는 메타데이터입니다. 여기서는 Name 태그에 "allow_web" 값을 부여하였습니다.
"sg_web"이라는 이름의 AWS 보안 그룹을 생성한다. 이 보안그룹은 모든 IP에서 TCP 프로토콜로의 수신 접근을 허용하고, 모든 IP로의 모든 프로토콜 및 포트로의 발신을 허용하는 설정을 가지고 있다. (원래 이렇게 다 오픈해놓으면 안되지만 실습 상황이므로 전체허용을 해놓았다.)
4. 인스턴스 정의
resource "aws_instance" "example-2a" {
ami = data.aws_ami.amzn2.id # 이전에 정의된 aws_ami 데이터 소스에서 amzn2 AMI의 ID를 참조
instance_type = "t2.micro"
key_name = "tf-key"
vpc_security_group_ids = [aws_security_group.sg_web.id] # 이전에 정의된 aws_security_group 리소스에서 sg_web 보안 그룹의 ID를 참조합니다.
subnet_id = "ap-northeast-2a의 서브넷 id"
availability_zone = "ap-northeast-2a"
user_data = file("./userdata.sh")
tags = {
Name = "Terraform-ec2-2a"
}
}
resource "aws_instance" "example-2c" {
ami = data.aws_ami.amzn2.id
instance_type = "t2.micro"
key_name = "tf-key"
vpc_security_group_ids = [aws_security_group.sg_web.id]
subnet_id = "ap-northeast-2c의 서브넷 id"
availability_zone = "ap-northeast-2c"
user_data = file("./userdata.sh")
tags = {
Name = "Terraform-ec2-2c"
}
}ap-northeast-2 리전에 있는 두 개의 다른 가용 영역(2a와 2c)에 EC2 인스턴스를 각각 하나씩 생성한다.
두 인스턴스 모두 동일한 AMI, 인스턴스 유형, 키 이름, 보안 그룹 및 사용자 데이터를 사용하고 있다. 차이점은 다른 서브넷, 가용 영역에 위치한다는 것이다.
user_data는 EC2 인스턴스 시작 시 실행할 스크립트를 지정할 수 있다.
./userdata.sh라는 파일을 생성해서 user_data의 값으로 지정해준다.
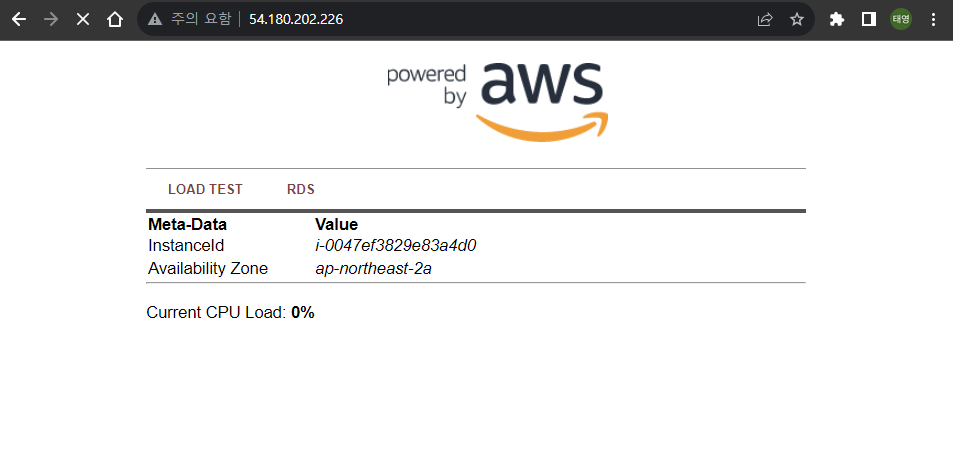
5. user_data 스크립트 생성
#!/bin/sh
# Install a LAMP stack
amazon-linux-extras install -y lamp-mariadb10.2-php7.2 php7.2
yum -y install httpd php-mbstring
# Start the web server
chkconfig httpd on
systemctl start httpd
# Install the web pages for our lab
if [ ! -f /var/www/html/immersion-day-app-php7.tar.gz ]; then
cd /var/www/html
wget https://aws-joozero.s3.ap-northeast-2.amazonaws.com/immersion-day-app-php7.tar.gz
tar xvfz immersion-day-app-php7.tar.gz
fi
# Install the AWS SDK for PHP
if [ ! -f /var/www/html/aws.zip ]; then
cd /var/www/html
mkdir vendor
cd vendor
wget https://docs.aws.amazon.com/aws-sdk-php/v3/download/aws.zip
unzip aws.zip
fi
# Update existing packages
yum -y updateAmazon Linux 2 AMI에서 LAMP(Linux, Apache, MariaDB, PHP) 스택을 설치하고 설정하는 스크립트이다.
이 스크립트는 테라폼으로 생성된 새 EC2 인스턴스에서 실행된다.
로드밸런서 생성 및 연결 작업은 다음 글에서 이어서 작성하겠다! 👾
'DevOps > Terraform' 카테고리의 다른 글
| [Terraform] 2. 로드밸런서 생성 및 연결 (0) | 2023.08.08 |
|---|

댓글